FFFjacking (EN)
Autor: .cCuMiNn. | 2.6.2011 |
Description of new hacking technique, which allows data hijacking from victim's local disks or upload and run files to victim's computer (depending on used OS and web browser).
What everything attacker can?
Attacker can reach the following (depending on used OS and web browser):
- read directory index of user’s computer disks
(a lot of web browsers) - read content of text-based files stored in user’s computer
(a lot of web browsers) - get some file from local disk of user’s computer
(Windows XP + IE) - upload some files to some folder of user’s computer
(Windows XP + IE) - enable to start the uploaded files in user’s computer
(Windows XP + IE)
Potential of FFFjacking attack is very high and dangerous.
How to use the FFFjacking?
Here is necessary the participation of victim. I would like to compare this technique to clickjacking. For data hijacking is used drag&drop method like in cookiejacking published recently by Rosario Valotta.
Hijacking of directory index and content of text files
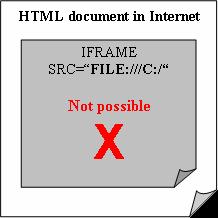
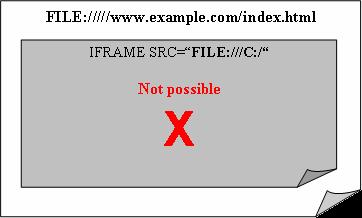
When you put the path to root directory of local disk to web browser address bar (for example FILE:///C:/ in Windows), web browser shows directory index. When we could use this address into attribute src of tag iframe, we could hijack data by drag&drop method. But web browsers can’t use frame with FILE: source in HTML document.
For example:
<IFRAME SRC="FILE:///C:/"></IFRAME> This usage is not possible in HTML document via HTTP protocol. It will return empty frame and error message.
It is very interesting, what web browser do, when we load this HTML document via FILE: protocol. We will start SMB server (Samba) on internet server. When we load this HTML document via FILE protokol, we can use also local source in frame atribute src, for example src="file:///C:/". Various web browsers work differently.
Behavior of Firefox and Chrome
These web browsers don’t enable using of FILE protokol in HTML document via HTTP protokol in source of tags like <iframe> or <a href="file://///www.example.com/index.html">link</a>. We can write this FILE URL directly to address bar of web browser or send the link via e-email to user's mail client software. When web browser load HTML document via FILE protocol, it can shows frame with local content.
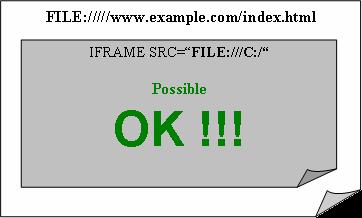
It is possible to evade security limitation and show directory index or content of local text-based file in frame.
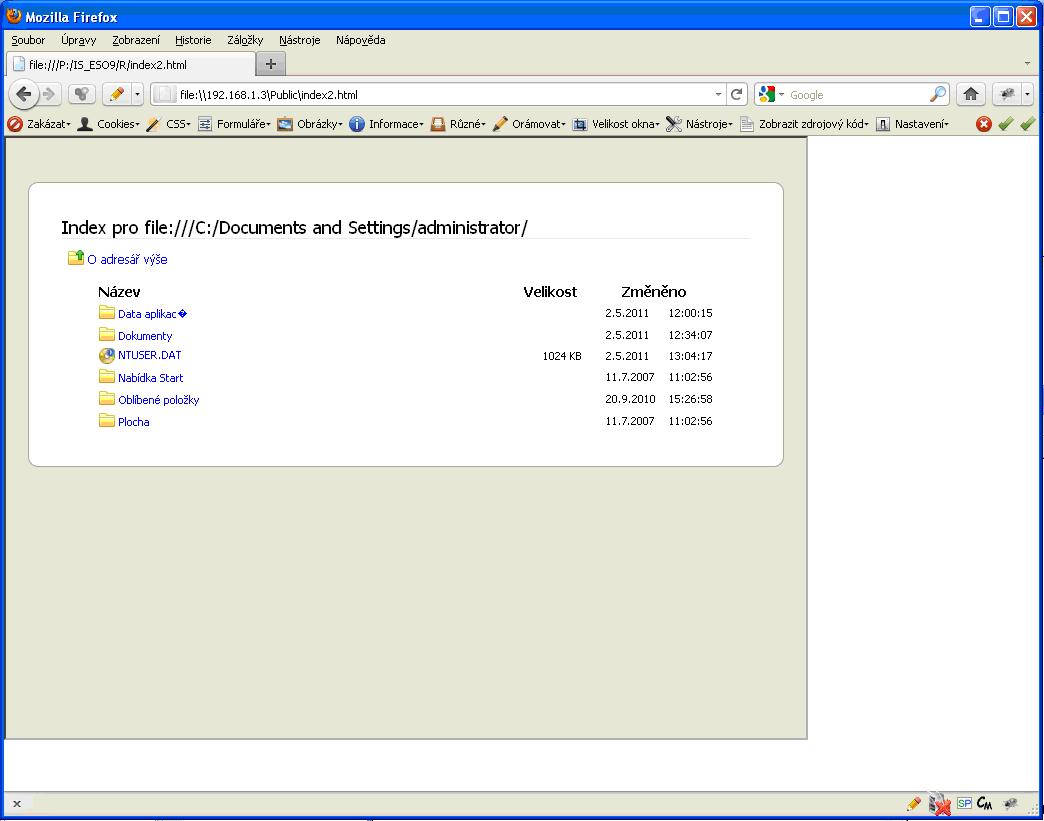
But…how can we get content of frame? We can’t access to the frame, because Content Security Policy exists. Now comes method drag&drop. User drag content in frame unawares and drop it to the object textarea in attacked HTML document. I will not describe this method in detail here, because it already wrote Rosario Valotta in his article about cookiejacking. For example we can use easy web fake game in style: click here, press CTRL+A, press CTRL+C, click here, press CTRL+V…
Behavior of combination of Windows XP and IE(6,7,8)
We can’t load the local content to frame in Internet Explorer even when document is loaded via FILE protocol.
But Internet Explorer allows load the local content through shared folders, for example FILE:\\127.0.0.1\C$. Even it is possible to view shared content in HTML document loaded via HTTP protocol.
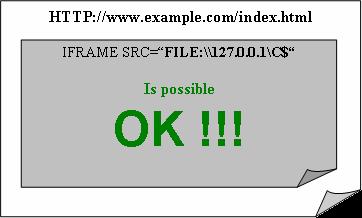
For example:
In combination of Windows XP and Internet Explorer is interesting, that it doesn't show directory index in frame only, but it shows all the Window Explorer. It can be very dangerous.
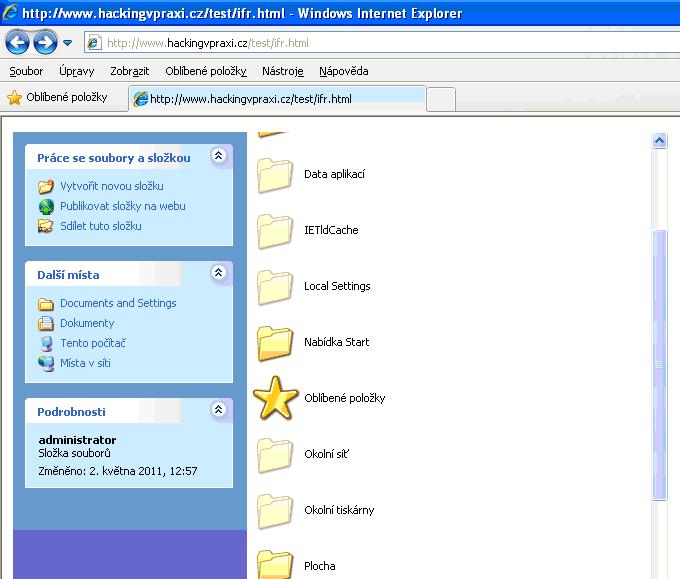
Other web browsers allows drag and drop directory index or content of text-based file to textarea object. But it isn’t possible in Windows Explorer. Attacker must go in other way. He will share dictory in SMB server for writing. Then it is possible by means of trick CTRL+C and CTRL+V copy local files (directories or all disks) to shared attacker’s folder. This way doesn't copy only files names, but copies the whole files to the attacker’s server.
It is possible to do it also by contraries. It means to do copy of file from shared folder of attacker’s server to the user's local disk. Attacker can select local folder of user's computer for upload attack files. I will show PoC 0-day exploit in the end of this article. This PoC will do copy of executable file from attacker’s server to folder "C:\Documents and Settings\All Users\Start Menu\Programs\Startup" in user's local disk. Try tip, what will happen after computer restart :)
When the sharing of local folder doesn't run, attacker can show his shared folder in frame. Windows Explorer provides menu with many possibilities. You can use clickjacking method to convince the victim to click to the link „This computer“. It will show list of local disk, etc. Windows Explorer provides many possibilities for attack. It only requires your fantasy. But many of these methods (for example using of context menu) are following with warning messages.
How can the attack look like in practise? I imagine web application, which learns users the basic work with computer. It learns them to copy the files, sharing of folders or formating the disks :)
PoC (0-day exploit) Windows XP + Internet Explorer
Index.htmlifrAttacker.html
ifrLocal.html
Related documents:
Security of browsershttps://docs.google.com/present/view?id=dcm4kmp7_18w8945rdw
Cookiejacking
https://www.swisscyberstorm.com/speakers/valotta-slides
Budeme potěšeni, pokud vás zaujme také reklamní nabídka